k8s kubernetes Lesson 6 yaml docker-registry cron part 2 No minikube
normal k8s
https://sueboy.blogspot.com/2019/11/kubernetes-nodeport.html
namespace docker-registry
{
"kind": "Namespace",
"apiVersion": "v1",
"metadata": {
"name": "docker-registry",
"labels": {
"name": "test-dev"
}
}
}
secret.yml ID/PWD:username/password tls:cn=docker-registry
apiVersion: v1
kind: Secret
metadata:
name: registry-tls
namespace: docker-registry
type: Opaque
data:
tls.crt: LS0tLS1CRUdJTiBDRVJUSUZJQ0FURS0tLS0tCk1JSUVzRENDQXBnQ0NRRHpteitOQUZCMGRUQU5CZ2txaGtpRzl3MEJBUXNGQURBYU1SZ3dGZ1lEVlFRRERBOWsKYjJOclpYSXRjbVZuYVhOMGNua3dIaGNOTVRrd01qSTJNVEF3TlRBMldoY05NakF3TWpJMk1UQXdOVEEyV2pBYQpNUmd3RmdZRFZRUUREQTlrYjJOclpYSXRjbVZuYVhOMGNua3dnZ0lpTUEwR0NTcUdTSWIzRFFFQkFRVUFBNElDCkR3QXdnZ0lLQW9JQ0FRRFBKcHhZK0RVQ05aMVh4Tkc0bUJlaFp2ZXZ4R21XMFdZandhRklzcFQ0L09ETWgwZVgKRXRmT0xpaUZibXFzMi93L01CeWlUSWlZczltMFdhdG5uVDc5bm5wZUVHdFNtQUJHeXMyU1hxdDZ3SzJubHJSLwowVllaVEpJQ2t2amE5WExtQ2w2eEgrbFFxWVFnNHlHSWxuZ2ZXUFBCTzkvVFhnS2Jmc2xBTk9uTXY0ckVTMlNFCkZLQzNuSTRqY1JWc1BQSUNkNDNJVlU1akNiRllublZJS2l2eTdqY0l0Q2JoelZsTHRuOHFIRE5YcElHSlpTTlYKUkdSdUVhN3ZFbUloei90blJZdFJRTmpSNGhQNkM5eG1QMFpBZFhjQWZYMTk0aVVKNDRFYnZUZ0NKK0I4Yi9jdwpEZ29IRWxCbGtJaUtmSm9wL0RhR3B5OUY0VjRhbHZIcnNMdFdYYTZYWmQzeGxmWWx6S2xMZ0IzTDJVQ2VCUWljCk0yUDlXMEZZZGFIR3NjUkFyNGQvbEtiZE1PYXNDV2dXaHlGekRDMUFYQkcxdU9SSXFBbi84OTJPQnk1UVE2SDQKSk9yOXNRRGhRejVEdWZReFlGNDZUZjZUNk9MOGp6TkUrUk11YmR2RmVVS1ZwYzJXazgrVWY3UE9OdW9iRC9XZgpTRFVCYjNsSCtGVTFZalVhR0Y5VzNwSE14NXZzTU8xOFJ3UTIzU2ZFT1dMZFFseU8rYXg3STZKVm5CbG1xaStFCk16QjFHMzVTbmlMMWcyVDRkbFlIWThIbllaU1A3RFdYR3JrZ2l6SloweUUveE55dkJuLy9GeWtIYTlIdjBhUk0KNE45OUhHRkthTmNzdkFDR2NSU2QvYUdHUDdqWHNEb3R2R1U5VjU4ems2S21oVGRjN3V0cE9Hb0Nud0lEQVFBQgpNQTBHQ1NxR1NJYjNEUUVCQ3dVQUE0SUNBUUM4U1orN0V3U0liY0tDT0xoV3NvbDEzNUVIYVdiRTEzOFRRdHBVCk55aExqZXM3THVQSjg3YVdjK0NWT3VMWEdIY2FtTiszQWhKL1k3L1U5NlVCWS8yTDREUnd6b0RDYzhhQ3ZQY0oKZDhWcGxvUXJuRzRueUgxVTJUV243SXo1UDNrYjVZeE82UHlVdlNZMTJTaXBxWmVuQU1STzVQSDRlUldwbDkwbAp3cHJDVU1TNGhaL3FGVE1ORG1HSzBGS243VHZRekZrSVo1eEhUK0VncTNzcERVY1BCenV4WVdGTG9pT2ZGUFRZCnZkSDc5Vis5K1p6T3ZBVlF3ZHhHSVlOaGlpNGd1OTg4N3Jld3RKbEZUQ1pXT05DWnNMcUw0RHBtWmJhbUlxRi8KakF5ZUR4T2kwN2VKcTlUREFLUlErZzg1NzMvR2JhVU5MVHVndzM0Z1pNZUttUnNzUjBEZWc5ckFHeXRRM2pqRApqeWJLYmo1SE8vT25xNTlGSk9rRi94eklZYWtXcjVPem1kRzJDdVhNOXhSN3BYSm5IM0RKcWUwc2FQd2ZMV2xPClF3L1RRM1lpMHg4ajhwOTRpeHZWbnRPRFRIUXBmeUFDMDloaFNmVG1sMnJXT3FqTzJ4d1dzUkhEOXBUQ0FpMG0KTHlZQS9UTVVXRWdMdklmMEZjOXRZZGkrck9HQVJuRWdXdjdhRjhKL0pRUlZ2ZjBVL2hGTmo4bFRmY0RuOU95WQprVEtWdHNRVllqZXNBU1lIdzYyRmZoUkRIZmZRbUlscTN3emljU3MvbnBQMzZraExCZGt0TnZzakVNaE40a0JLCjR5NlJWekdZR20rakpVQk8zV3ZQbHF0T0pwVUFCbHVCWFZOK3hhMnZOODNGYjZtMFlJTmVWbXNFQmxnVTVGT1oKa2xFVTJ3PT0KLS0tLS1FTkQgQ0VSVElGSUNBVEUtLS0tLQ==
tls.key: LS0tLS1CRUdJTiBQUklWQVRFIEtFWS0tLS0tCk1JSUpRd0lCQURBTkJna3Foa2lHOXcwQkFRRUZBQVNDQ1Mwd2dna3BBZ0VBQW9JQ0FRRFBKcHhZK0RVQ05aMVgKeE5HNG1CZWhadmV2eEdtVzBXWWp3YUZJc3BUNC9PRE1oMGVYRXRmT0xpaUZibXFzMi93L01CeWlUSWlZczltMApXYXRublQ3OW5ucGVFR3RTbUFCR3lzMlNYcXQ2d0sybmxyUi8wVllaVEpJQ2t2amE5WExtQ2w2eEgrbFFxWVFnCjR5R0lsbmdmV1BQQk85L1RYZ0tiZnNsQU5Pbk12NHJFUzJTRUZLQzNuSTRqY1JWc1BQSUNkNDNJVlU1akNiRlkKbm5WSUtpdnk3amNJdENiaHpWbEx0bjhxSEROWHBJR0paU05WUkdSdUVhN3ZFbUloei90blJZdFJRTmpSNGhQNgpDOXhtUDBaQWRYY0FmWDE5NGlVSjQ0RWJ2VGdDSitCOGIvY3dEZ29IRWxCbGtJaUtmSm9wL0RhR3B5OUY0VjRhCmx2SHJzTHRXWGE2WFpkM3hsZllsektsTGdCM0wyVUNlQlFpY00yUDlXMEZZZGFIR3NjUkFyNGQvbEtiZE1PYXMKQ1dnV2h5RnpEQzFBWEJHMXVPUklxQW4vODkyT0J5NVFRNkg0Sk9yOXNRRGhRejVEdWZReFlGNDZUZjZUNk9MOApqek5FK1JNdWJkdkZlVUtWcGMyV2s4K1VmN1BPTnVvYkQvV2ZTRFVCYjNsSCtGVTFZalVhR0Y5VzNwSE14NXZzCk1PMThSd1EyM1NmRU9XTGRRbHlPK2F4N0k2SlZuQmxtcWkrRU16QjFHMzVTbmlMMWcyVDRkbFlIWThIbllaU1AKN0RXWEdya2dpekpaMHlFL3hOeXZCbi8vRnlrSGE5SHYwYVJNNE45OUhHRkthTmNzdkFDR2NSU2QvYUdHUDdqWApzRG90dkdVOVY1OHprNkttaFRkYzd1dHBPR29DbndJREFRQUJBb0lDQVFDb0FkZXliUFNKS3pUR3Q1R2tsbTRyCjhKZ1lUVU9hRjVFd2xOMmJXWU5yZ2FWTkhMYmFkMlRpQ3h2QVJISnVhaWpta3IzV2dCNFZRMkRoWGd5Zmg3Qk0KQUZtY3F0SndkV2xjQVNYRGZkYTBRMHRVYmUxTThWcFVRSDczYVg0K0QrNDFWdG0vN0hMTmdmN3dzV1pFSWsyZwpsd056aUgwYkw5Y0xpRVB2T0RzYlhZcE5kQnc4NTRJR0NRcGJBbDl1bnV0bFJ0T09WR216OTJ1SHhWUzN4OFJIClRoOENoeUkxNXRkeWlid1BTam4xN2kxRll1cktRQ0w0Qm8yTHhxd2lZazJ6VDNzVDFuVkRuSW01Tmg5MktnRnYKVEJYTkp2bzl1OGx3Z0x6NDQzbG1mak1hbWJDd24rSlFJL0Zpdmx1UGZrbUduZEVYV3NjRGRTcGVoR2dIVVJwTwpGWURKU29jaTlGVG5NRTF4a3c4TUR5V1JjSzdvSjJrRzd0RXh4aDBML1NjK1dmY2RKVFJyRW9BR3VxNzNYdWZGCk1CdVRoK3JCVU9ITVpSTVJMTXN6aGVTekp1SXBZU1BsNUF1VUY5cHVNd21vYkFpbXBzdmpQVEprRlR3bytLdmQKYUVlNW5IMFlmTlRNS3JSU1YybjBaTmp0dHB3VU9VZ2lXVE9VdnJXOGNiMlVJZjRpRVk3VjJBc3ArKzVvK25QdQpZRkdiZWd0d1U3dURyNTN2YjNPRE9ZRVUrUlZmYTlScWxXMUswYlpmeGZBcCtzdVNQTHczclBiNk4xZ0UybWhFCnNUcy9FYmQ5dW5Vdm1XZ0tzdGtBeDBuRVM4Z1VqNW9Zc1F5Um1wM1NaaUJXUmlXYnZoSzRaQ3k0V3NaZUZWZEoKMEtuNDZCeXB1Sndtelozd2hRMDBZUUtDQVFFQS9XODlsa0c1eW9UVXlEZnI3M0hqMHNyZ0o3amlLdlNoZ29PVwpCck1ndkxxeEMzUVRaZjg2VHpObnhoVDFwSS9sUnNRN2tiYjJhclpHZ3phRHlNemV2QXpYMUJiNnRkakxnVVIvCi9ZMTR1QW9VVzhYNEhrY0Rhb2xtVkFjOXdsRmpJcHVjY25YdEZJZ3NacnVydEJSQW9mSU91aUV4bzJCQkc3aUEKMW1qN2RqZlZwSTQzWWd4UHBiZndmVjV0bC9CTENMQis0RzZkclhvaExBdTlqSWlKNWw4MEEydG1qR3Z3S3lVTApHc3RGamc1MVcxTjQyTC8rY0FSQ213a3pUUTkwMFZaS1BaOUdtZTE2NndZdjl4eXdsZjN6L09udGJsZjRLaXE4ClVVQXR3RFF3bWFwN3o1OUhpckp1TEczMDk3QWRlNTZjQ1JOMk53c0YzYTJQM09VeFVRS0NBUUVBMFQ5dHlzK24KVHdkd0JNK0lRcVBQUWt0ZjhodENSUW1Wamw0WWVZc1ptR0F2TXRqN00wYVhjcnVLT0k2VjBmc0k2T0RrbWRDSQpnZWYwUk15WXR3czdMcGtXWmIyQzlFdzk0K3VpL2tEQVlxUUJXczBVaTQwbTdNeDgwN2pKdGZONVJad3d1MGxNCm1kR1ZSa3hkbWVtM0V6MmhsR2ltZUMvcnB5REtiMkY1SU9Mdjk1cUdlWHBlOGNwUDhVMDd6dTdqdmdDNVRSeDcKV0pYYVVFSEt4bjVHVHU2UUluMXQrZmw5MnRnNXprNmNjaklUeStvUG4yNWU1ZnR3ZlNaVzg1Tno2dFQzRE04bwpMZ0h4aFBNS0RzcjZySnVRSExObHI1MnY4TDlwVlZlWlpOanlmbDNxUmhqOE5zanN4OEhCczV1Z1ZFYU9MWkJTClFrU1pCYzNkYldONDd3S0NBUUFMWVhaemkrb0s5U0lWQjZYWnI5U2FQN0FIT0o4M2JKcmdJSWFaTUd3VTdaRkwKd1YrcG9lZDliUUtJKzZINFRObnY3cG42Tml3a3FLREwvYU8zWGJQVzRBREZMbTc5d1ltSitZaUIyMXVEY0RodgowcGtNeXdXVlFDeFBNN0FMVE5wVjBJVWJBcjZ0d0Z1MkZWRmxtYzg1Tm9TQXlVTFFZbDhxSG9QeW5PNUY1Y1g3ClNNT2w3SVdiSElKNUxzZGZIbFJRUkpTK0FWbWxVNm12cjZ0SVowMUNBaDUwMU5yYkRYSFFqaTVNZXJwWjRiNVYKWm84enRKTjVka2VEYk10WDk0eTRaZGFabzlCbzB5aEU2NWMxMHB6L2IxTUlsWHlyQ3RwREVuNDRhOWhpSERYZQpnTEJrcDNOd0FBbEFoNE9McCtYN0NpbFpvdjBaQmE2eXdMdUlJT2F4QW9JQkFILytaSkppWXQwY2w1RFp3V2ZCCis4MTVmYjhDblk3TlJnWkgySURBYlcrZnBqOWNLb3c2NmZqc2JxZ1p6OXNaeTJGbjcyMkcrWGs5QVZYME1KWUcKOExTWVAvTUw4VWF1UEUxbW5kVVlscFcvN0hRMmJoTE96TGljZk42bGNmMHlhVVFEUG12UmNtSEVxYUxPbzVLNgpPNW94WU56L0JwVU4rdi9JTnd2YWU5VjUrMzlocmxBd1lsTlVoWUg4MUZESUg5YmhhbmVZckhxTGIzY1lSNGtUClJMNlRmdWNhQW1PZUVUWUVmWmVNem5XcjNDQW5sRmJabElMcFF1M0t2ZlZRaE45b1ZaWW9RVk9qTExFK1dUQ2oKU0tLOHBYSm82aEo2U2x6aE9QVlRHQ2x2NnlVUkhYU3pZOU8vSTljczFlZWZrbnI2alkyaGNpL0c5ak51c2J0dgoxVkVDZ2dFQkFJVUdEbEcxQmpPdTVhcVZ1eDZzTzUwbHB4eVpienFvMm1TRVMwZHNYNDcvclN6ZGRoblE4QnVVCjlURHF3aDBlM0pZdGlUczM4Z21RT1pVdndEM2FnNjdDU0t1T3FNUWM3aU00S01rbmdrakxOMnhIM2luYjZxUjMKc0ZLYVluWDlMdTBZeVVZU013cGwyNjM4ZHoxanY3a05wRE8xd2p0bTh5TjdxQk00d3IrU3JNV0EyWHlhSG1hZgpBZE5hNzdxdHppL0JIcXdVTFZsbDFTSitIU1dqdHU2QmRNQTlLandzMllieWxUTm1UbmZWTzdLeVMzTFAwY2xCCm1MaEVhYS93d2J1Mm5sTWRxdDJpeTQzcE5QYmhRZ0lOck95dDR6cXhNZEVXdWtSeHAwSGFieXdFcldFWXJFQ1cKdS90ZDhKZ291QmZqZ0JDQ3hnNjNvWlJVS1ZnU1FQST0KLS0tLS1FTkQgUFJJVkFURSBLRVktLS0tLQ==
HTPASSWD: dXNlcm5hbWU6JDJ5JDA1JGprbU5CSm1DVTYyV0pKc0tqcWx3RC5BQmpLcUswc2R0SU9lZ29kb3VrQzFpR0owc05ENjhD
configmap.yml
apiVersion: v1
kind: ConfigMap
metadata:
name: docker-registry
namespace: docker-registry
data:
registry-config.yml: |
version: 0.1
log:
fields:
service: registry
storage:
delete:
enabled: true
cache:
blobdescriptor: inmemory
filesystem:
rootdirectory: /var/lib/registry
http:
addr: :5000
host: https://docker-registry:30500
secret: asecretforlocaldevelopment
headers:
X-Content-Type-Options: [nosniff]
Access-Control-Allow-Origin: ['*']
Access-Control-Allow-Methods: ['HEAD', 'GET', 'OPTIONS', 'DELETE']
Access-Control-Allow-Headers: ['Authorization']
Access-Control-Max-Age: [1728000]
Access-Control-Allow-Credentials: [true]
Access-Control-Expose-Headers: ['Docker-Content-Digest']
tls:
certificate: /cert/x509/public
key: /cert/x509/private
auth:
htpasswd:
realm: basic-realm
path: /auth/htpasswd
health:
storagedriver:
enabled: true
interval: 10s
threshold: 3
deployment.yml
apiVersion: apps/v1
kind: Deployment
metadata:
name: registry
namespace: docker-registry
spec:
replicas: 2
selector:
matchLabels:
app: registry
template:
metadata:
labels:
app: registry
spec:
#restartPolicy: Always
volumes:
- name: config
configMap:
name: docker-registry
items:
- key: registry-config.yml
path: config.yml
- name: cert
secret:
secretName: registry-tls
items:
- key: tls.crt
path: public
- key: tls.key
path: private
- name: htpasswd
secret:
secretName: registry-tls
items:
- key: HTPASSWD
path: htpasswd
- name: registry-data
emptyDir: {}
containers:
- name: registry
image: registry:2.7.1
ports:
- name: http
containerPort: 5000
protocol: TCP
volumeMounts:
- name: config
mountPath: /etc/docker/registry
readOnly: true
- name: cert
mountPath: /cert/x509
readOnly: true
- name: htpasswd
mountPath: /auth
readOnly: true
- name: registry-data
mountPath: /var/lib/registry
service.yml
apiVersion: v1
kind: Service
metadata:
name: docker-registry
namespace: docker-registry
spec:
type: NodePort
ports:
- name: registryhttp
port: 5000
targetPort: 5000
nodePort: 30500
selector:
app: registry
===== docker-compose =====
docker-compose.yml
version: '3.3'
services:
gethpeers:
build:
context: gethpeers/
image: docker-registry:30500/username/gethpeers
volumes:
- cronlog:/app/cronapplog:rw
- /etc/localtime:/etc/localtime:ro
networks:
- fastdev
fakelog:
build:
context: fakelog/
image: docker-registry:30500/username/fakelog
volumes:
- cronlog:/app/cronapplog:rw
- filebeat:/usr/share/filebeat/data:rw
networks:
- fastdev
volumes:
cronlog:
filebeat:
networks:
fastdev:
driver: bridge
fakelog/Dockerfile
FROM docker.elastic.co/beats/filebeat:6.5.4
COPY filebeat.yml /usr/share/filebeat/filebeat.yml
USER root
RUN chown root:filebeat /usr/share/filebeat/filebeat.yml
USER filebeat
fakelog/filebeat.yml
filebeat.prospectors:
- type: log
paths:
- /app/cronapplog/*.log
exclude_files: ['.gz$']
fields_under_root: true
symlinks: true
output.logstash:
hosts: ["logstash:5044"]
cron/crontab
* * * * * /app/run-cronjob.sh /app/start.sh > /proc/1/fd/1 2>/proc/1/fd/2
#* * * * * echo hello > /proc/1/fd/1 2>/proc/1/fd/2
cron/Dockerfile
FROM debian:stretch-slim
RUN apt-get -y update && apt-get install -y cron curl jq nano iputils-ping net-tools && \
rm -r /var/lib/apt/lists/*
ADD . /app
ADD crontab /var/spool/cron/crontabs/root
RUN chmod 0600 /var/spool/cron/crontabs/root
RUN chmod +x /app/run-cronjob.sh
RUN chmod +x /app/start.sh
CMD cron -f
cron/run-cronjob.sh
#!/bin/bash
if [ -z "$1" ] ; then
echo "need name of cron job as first argument" > /proc/1/fd/1 2>/proc/1/fd/2
exit 1
fi
if [ ! -x "$1" ] ; then
echo "cron job file $1 not executable, exiting" > /proc/1/fd/1 2>/proc/1/fd/2
exit 1
fi
if "$1"
then
echo "cron job $1 Run!" > /proc/1/fd/1 2>/proc/1/fd/2
exit 0
else
echo "cron job $1 failed!" > /proc/1/fd/1 2>/proc/1/fd/2
exit 1
fi
cron/start.sh
#!/bin/bash
# geth get admin.peers
IP_PORT=xxx.xxx.xxx.xxx.xxx
ETH_METHOD=admin_peers
PEERS=$(curl -X POST -H "Content-Type: application/json" --data '{"jsonrpc":"2.0","method":"'$ETH_METHOD'","params":[],"id":1}' $IP_PORT | jq -c '.result[].network + {"run":"curl json"}')
printf "\n===== Now Geth Peers =====\n"
#printf "Peers: %s\n" $PEERS
echo $PEERS | jq .
#echo $PEERS >> /app/cronapplog/gethpeers.log
curl -X POST -H "Content-Type: application/json" --data '{"jsonrpc":"2.0","method":"'$ETH_METHOD'","params":[],"id":1}' $IP_PORT | jq -c '.result[].network + {"run":"curl json"}' >> /app/cronapplog/gethpeers.log
===== push image to docker-registry =====
nano /etc/docker/daemon.json
{
"insecure-registries" : ["docker-registry:30500"]
}
service docker restart
docker login -u username -p password docker-registry:30500
docker-compose push
nano /etc/hosts
192.168.99.118 docker-registry
check https://docker-registry:30500/v2/_catalog
#check result
{"repositories":["username/fakelog","username/gethpeers"]}
IF get error
ERROR: blob upload unknown
when docker-compose push
Deployment replicase 2 -> 1
apiVersion: apps/v1
kind: Deployment
metadata:
name: registry
namespace: docker-registry
spec:
replicas: 1
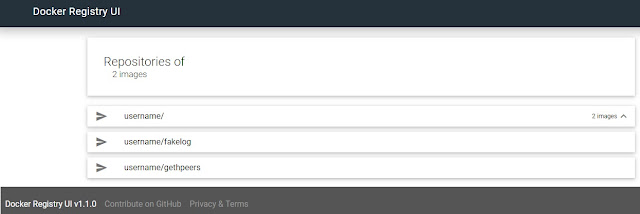
===== docker-registry ui =====
===== docker =====
docker run -d -p 80:80 -e URL=http://192.168.99.118 -e REGISTRY_URL=https://192.168.99.118:30500 -e DELETE_IMAGES=true joxit/docker-registry-ui:static
broswer http://192.168.99.118